The usage of wireless networks are becoming increasingly popular these days due to their operation flexibility and low cost setup. Wireless networks such as WLANs allow users to access network resources from anywhere in the campus using mobile devices like laptops and tablets. This offers a great deal of flexibility to students and employees, thereby eliminating the need to always stick to their desks during their work time.
However, on the flipside of all its advantages lies major security issues. As more and more companies have now started using wireless technologies in their network, these security issues puts the business on a high risk. As opposed to wired networks, wireless technology does not limit physical access to an outsider such as a hacker. Today, with all the readily available tools it is easily possible for the hacker to compromise loopholes in the wireless security system and gain access to the network.
We will look at some of the common vulnerabilities that exists in the wireless networking technology, ways to exploit them for gaining access and also the countermeasures for preventing them
WIRELESS NETWORK BASICS
Before jumping into the actual hacking, let us go through some of the basic concepts of wireless networking.
The wireless standard is commonly represented as 802.11 and is used to setup wireless local area networks (WLANs) in environments such as schools and offices. 802.11 standard has 3 leading protocols (or extensions) as follows:
1. 802.11a - It offers higher speed (up to 54-Mbps), more channels and less interferences.
2. 802.11b - This protocol is also popularly known as “Wi-Fi”. This is the standard that was used in most of the Wi-Fi hotspots.
3. 802.11g - This is similar to the 802.11b protocol but provides much faster transmission.
Components of Wireless Network
A wireless network comprises of the following 3 basic components:
1. Wi-Fi Radio Device: This can be any device that has a wireless card (NIC) built into it such as a laptop, tablet, Wi-Fi enabled PC or a cell phone.
2. Access Point: This is the device which allows Wi-Fi radio devices to connect to the wireless network using WiFi- standards. The AP then has a wired connection to the router. However, most modern routers now come with built-in APs to eliminate the need for an extra device.
3. Gateway: Routers are connected to the gateways which then connects the whole network to the Internet.
Detecting Wireless Networks (War-Driving)
To detect a wireless network such as a Wi-Fi Access Point, you can start roaming in a technology park, downtown area or simply through the walls of your own building using your Wi-Fi capable device (such as laptops and palm devices) with a “war-driving” software. Some of the popular war-driving software programs are listed below:
Netstumbler: This is a Windows based war-driving tool that can detect wireless networks and also mark their position with a GPS.
MiniStumbler: This is a portable version of NetStumbler that can be installed on handheld computers.
Vistumbler: This is another handy war-driving tool for Windows based operating systems.
Kismet: This is a Linux based wireless sniffing tool that also has the ability to perform war-driving.
Wifi Scanner: This is a GUI based Windows tool to detect all the available APs in your surroundings.
Please note that all wireless network cards (NICs) are not same and some may not be compatible with the above mentioned war-driving tools. In that case you will have to use the software that came with your wireless NIC for detecting access points.
WIRELESS SNIFFING
Wireless sniffing is no different than the “wired sniffing”. In this case the protocol used for sniffing is 802.11. Since radio waves are omnidirectional, it is easily possible to carry out a “man-in-the-middle” attack and capture all the packets from the wireless traffic available in your range.
Configuring Wireless Cards for Promiscuous Mode
Promiscuous mode allows the NIC (Network Interface Card) to capture all the network traffic that arrives at it instead of capturing only those that are intended for the NIC.
Unless your wireless card is configured to operate in promiscuous mode, it is not possible to perform wireless sniffing.
Most wireless network cards do not support promiscuous mode on Windows operating system and hence one has to use Linux to successfully perform wireless sniffing. If you still want to perform sniffing on Windows, you can use a special type of wireless card known as AirPcap which is far too expensive compared to normal ones. AirPcap cards can be used on Windows with sniffing programs like “WireShark” and “Cain&Abel“, but for all other cards one has to use Linux platform.
Tools for Wireless Sniffing
Let us look at some of the widely used tools for performing wireless sniffing:
Wireshark
Wireshark is one of my favourite packet sniffing tool as it is easy to use and supports GUI. Even though it works on Windows, I am using Linux operating system in my wireless sniffing demonstration as promiscuous mode is not supported on Windows platform. I am using TP-LINK TL-WN722N for this demo as it is fully compatible with Kali Linux that I am running it on. If you have a different wireless card or need to purchase one, please make sure that it is compatible with the Linux kernel that you will be using it on. Since Kali Linux is packed with Wireshark and all other useful tools there is no need to install it separately. Follow the below instructions to perform a sample wireless sniffing:
1. Boot up your computer from your Live Kali Linux DVD.
2. Once the Linux is loaded, plug-in your USB wireless card.
3. Open the “Terminal” window and type the following command:
iwconfig
4. If your wireless card is compatible, you should see your device listed as shown in the above snapshot as “wlan0”.
5. The next step is to put the card into the monitoring mode (promiscuous mode). For this, type the following command:
airmon-ng start wlan0
On my computer, wireless card is listed as “wlan0”. So, I have entered “wlan0”in the command. If your computer has a different listing such as “wlan1” or“wlan2”, then you need to replace the same in the above command.
6. After you execute the command successfully, your computer will create a new virtual wireless card and enable “monitor mode” in it. In my case it is “mon0” as shown in the below snapshot.
7. Now it is time to use Wireshark to start capturing the packets. To start Wireshark, click on Applications -> Kali Linux -> Top 10 Security Tools -> wireshark as shown below:
8. Now, from the Wireshark main window, select “mon0” from the Interface List, double-click on it and select option to capture packets in both “promiscuous mode” and “monitor mode”. Next click on OK.
9. Once you are done, click on the “Start” button to begin sniffing. This should capture packets from all the nearby available wireless networks. The following snapshot shows a sample packet capture:
The following are some of the other wireless sniffing tools worth considering:
Ethereal
This is another Linux based sniffing tool that works both on wired and wireless networks.
It comes as a built-in security testing tool in Kali Linux.
OmniPeek Wireless
OmniPeek is a commercial 802.11 sniffer tool packet with tons of useful features for network monitoring. It works on Windows platform.
WIRED EQUIVALENT PRIVACY (WEP)
WEP is a component of 802.11 WLAN networks designed to provide confidentiality of data in the wireless networks. Unlike wired networks where it is possible to limit physical access only to trusted users, the same is not possible in case of a wireless network.
Therefore, in order to overcome this limitation a special type of encryption called WEP is used to prevent attackers from intercepting the wireless data.
However, there is a clear weakness in the WEP security system that can be exploited.
Once enough data packets are captured and given ample time, the attacker can easily crack the WEP key used for encryption so as to decrypt all information back to raw data.
Cracking WEP Encryption
The following tools are used popularly for cracking WEP encryption key/password:
Aircrack-NG
This is a popular tool used on Linux to crack 802.11 WEP encryption keys. It is a command line tool that comes as a built-in feature in Kali Linux package and can easily be used by loading it from the live DVD. Since it takes a long list of commands and procedures to crack WEP passwords, I have decided to omit the demo of the cracking process from this book. But you can still Google for “how to crack WEP encryption” to find many step-by-step procedures that describe the actual cracking process.
WEPCrack
WEPCrack is another popular tool for cracking 802.11 secret keys. This is the first tool to give a public demonstration on how WEP encryption can be exploited.
WI-FI PROTECTED ACCESS (WPA)
WPA is another wireless security standard that was mainly developed to address the shortcomings of WEP. WPA uses a different encryption standard which is better than that of WEP and is designed as a software upgrade.
However, a flaw in this security feature called Wi-Fi Protected Setup (WPS) allows WPA passwords to be cracked using brute-force approach. Most access points have WPS enabled by default and hence remain vulnerable.
Cracking WPA Passwords
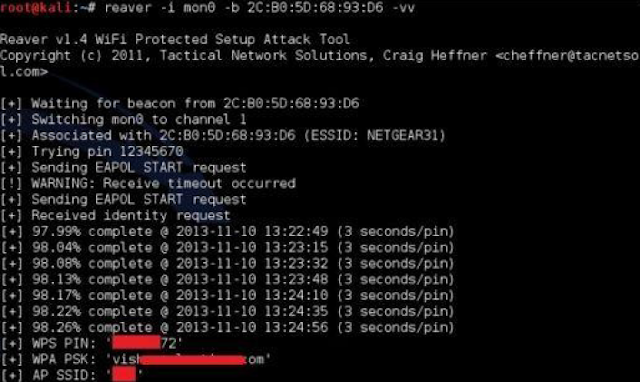
Here is a step-by-step demonstration of cracking WPA password using the Reaver tool that comes with Kali Linux.
1. Boot your computer using the Kali Live DVD and also plug-in the USB wireless card.
2. Open the terminal window and type the command iwconfig to make sure that your card is detected.
3. Once you see your card listed (wlan0) as shown above, type the following command to put your card into the “monitoring mode” and start using it.
airmon-ng start wlan0
This should activate “monitoring mode” for your card. On my computer it is enabled on “mon0” as shown in the below snapshot.
4. Now type the following command to detect nearby WPS enabled access points.
wash -i mon0 -C
This should perform a scan and list all the nearby access points as shown below. Once access points are detected, press Ctrl+C to stop the scanning process.
reaver -i mon0 -b 2C:B0:5D:68:93:D6 -vv
Please note that you will have to replace“2C:B0:5D:68:93:D6” with the BSSID of the target AP in your case.
6. The cracking process will take a few hours to complete and if everything goes well you should see the cracked PIN and passphrase in the results as shown in the below snapshot:
Other Tools for Cracking WPA
The following are some of the other WPA cracking tools that you can try:
coWPAtty: This is a Linux based tool which uses dictionary approach and precomputed hash files (similar to rainbow tables) to crack WPA passphrases.
Hashcat: This is one of the fastest CPU-based password cracking tool which uses different approaches like dictionary, brute-force and hybrid types of attacks. It comes for both Windows and Linux operating systems.
DENIAL OF SERVICE (DOS) ATTACKS
Just like wired networks, wireless networks are also susceptible to denial of service attacks. Since WLANs use radio waves on public frequencies for sending and receiving the traffic, it is easy to use other traffic from the same band to cause interference. If the attacker fails to gain access to the network, he may use DoS as a final option to attack the network. DoS attacks cause all the existing connections to the network to get dropped and also prevents new connections from happening thereby causing the WLAN virtually unusable.
Tools for Wireless DoS
Kali Linux has a handful of built-in tools and features to cause DoS attacks on WLANs. Most of these tools works by sending de-authentication packets instead of authentication packets to access points which causes the network to drop all the existing connections.
Other way to flood network is by sending authentication requests to APs with inappropriate status codes or random client MACs.
Some of the popular tools for wireless DoS include Void11, Fatajack and FakeAP (for spoofing or creating large number of fake access points in an attempt to confuse clients).
COUNTERMEASURES
The following are some of the countermeasures that one can employ to prevent possible attacks on a wireless network:
MAC Address Filtering: This feature uses a pre-defined list of MAC addresses of the clients’ wireless NICs who are allowed to connect to the network. This way it is possible to prevent strangers from accessing the WLANs.
Hidden SSID: Preventing an AP to stop broadcasting its SSID makes it go invisible and hence becomes inaccessible to attackers.
WPA instead of WEP: Since WEP has well known security issues, it is always safe to use alternate encryption standards such as WPA or WPA2 over WEP.
Disable WPS: Since WPS (Wi-Fi Protected Setup) is said to have flaws, enabling it makes WPA vulnerable. Therefore, it is necessary to manually disable the WPS feature where in most routers it comes pre-activated by default.
Firewall: Using a firewall with strong rules helps filter unauthorized traffic and prevent brute-force attacks.









0 comments:
Post a Comment